Security and Operations
Woot Math is dedicated to making sure your data is safe, secure, and always there when you need it.
Woot Math's cloud servers and services are located in state-of-the-art AWS data centers. AWS has many years of experience in designing, constructing, and operating large-scale data centers.
Woot Math's systems are architected for high availability; its core systems are deployed in N+1 and N-to-N redundancy configurations; and the system is protected against single points of failure. Woot Math maintains its servers and stores its data within multiple AWS availability zones. Each availability zone is designed as an independent failure zone. This means that availability zones are physically separated within a metropolitan region. Availability zones are all redundantly connected to multiple tier-1 Internet providers. In addition to discrete uninterruptable power supply and onsite backup generation facilities, each is fed via different grids from independent electrical utilities. Because of this architecture, Woot Math is resilient in the face of most failure modes, including natural disasters or system failures.
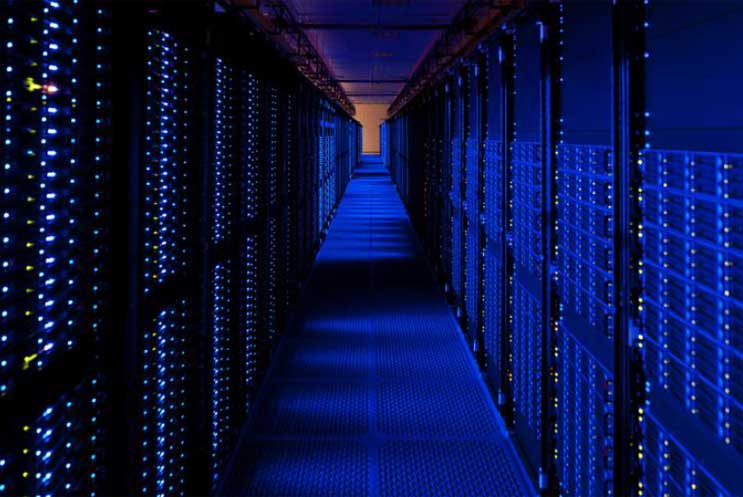
Woot Math has, in addition, a comprehensive disaster recovery strategy. We have push-button automation to stand-up and tear-down of our entire production server and service environment, and we can quickly and easily build out our infrastructure as needed in new geographical regions. We routinely test our disaster recovery capabilities by standing up new servers in a new data center and restoring all data from backup. Nightly backups of all customer data are securely stored in multiple geographic regions within the US.
Changes to Woot Math systems are typically pushed into production in a phased deployment sequence, with careful monitoring and testing throughout the phases. Rollback procedures for productions deployments are automated and documented.
Woot Math Has a Comprehensive Security Program
Woot Math’s engineering and operations teams are trained and experienced with respect to state-of-the-art security mechanisms and policies for cloud-based services. We employ engineers and managers who have worked in other domains with critical security and availability concerns including military systems, satellite communications systems, Department of Energy research systems, and the website operations of large multinational companies.
We routinely audit our systems for security vulnerabilities, proactively monitor security-related websites and other outlets for information on new vulnerabilities and best practices, and make system updates as needed.
AWS data centers (and hence, all Woot Math production servers and services) are housed in nondescript facilities. Physical access is strictly controlled both at the perimeter and at building ingress points by professional security staff utilizing video surveillance, intrusion detection systems, and other electronic means. Authorized staff must pass two-factor authentication a minimum of two times to access data center floors. All visitors and contractors are required to present identification and are signed in and continually escorted by authorized staff. When a storage device has reached the end of its useful life, AWS procedures include a decommissioning process that is designed to prevent customer data from being exposed to unauthorized individuals.
Network devices, including firewall and other boundary devices, are in place to monitor and control communications at the external boundary of the network and at key internal boundaries within the network used by Woot Math's systems. Woot Math uses a wide variety of automated monitoring systems to provide a high level of service performance and availability. Woot Math and AWS monitoring tools are designed to detect unusual or unauthorized activities and conditions at ingress and egress communication points. These tools monitor server and network usage, port scanning activities, application usage, and unauthorized intrusion attempts. Our systems are extensively instrumented to monitor key operational metrics. Alarms are configured to automatically notify operations and management personnel when early-warning thresholds are crossed on these metrics. AWS security monitoring tools help identify several types of denial of service attacks, including distributed, flooding, and software/logic attacks. Woot Math and AWS have additional protections in place against common attack vectors including Distributed Denial Of Service Attacks, Man in the Middle Attacks, IP Spoofing, Port Scanning, Packet Sniffing, Injection Attacks, and Cross-Site Scripting Attacks.